Server
About the Server tab
The Server tab allows you to view servers that have been scanned and registered. You can view servers within a group, register pseudo-servers, and register network devices.
Server List
In the server list, you can view the scanned servers in a list.
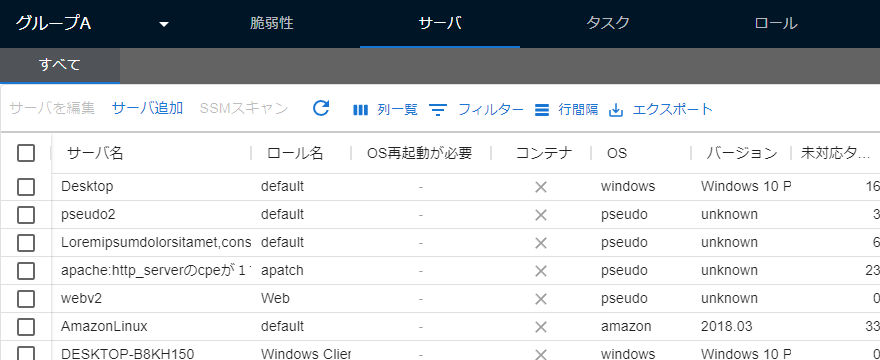
You can customize the order and display of the columns in the list.
| Field | Description | Update Timing |
|---|---|---|
| Server name | The name of the server. The initial value is set in config.toml at the time of scanning, and can be changed on the screen after registration. |
When updated on the Details tab. |
| Server UUID | The ID that uniquely identifies the server. | N/A |
| Server ID | The management ID of the server used in REST API and other operations. | N/A |
| OS restart required | Whether an OS restart is required or not. | When scanned. |
| Role name | The role to which the server belongs. If not set, it will be assigned to the “default server role”. | When updated on the Details tab. |
| Container | Whether it is a container image or not. | When scanned. |
| OS | The server’s OS. | When scanned. |
| Version | The version of the server’s OS. | When scanned. |
| EOL | The EOL of the server’s OS. | When scanned. |
| Platform | The platform, such as AWS. | When scanned. |
| Instance ID | The ID on the platform (such as AWS) if there is one. | When scanned. |
| IPv4 | The server’s IPv4 address. | When scanned. |
| Total task count | The total number of tasks associated with the server. | When scanned. |
| Unresolved task count | The number of tasks associated with the server that have a status of “NEW” and no hidden setting. | When scanned, and when updated on the Task tab. |
| In progress task count | The number of tasks associated with the server that have a status of “INVESTIGATING”, “ONGOING”, or “DEFER” and no hidden setting. | When scanned, and when updated on the Task tab. |
| Resolved task count | The number of tasks associated with the server that do not have a status of “NEW”, “INVESTIGATING”, “ONGOING”, or “DEFER”, or are hidden. | When scanned, and when updated on the Task tab. |
| Server tag | The tag set for the server. | When updated on the Details tab. |
| Server type | The type of server. | N/A |
| Scanner installation location | The location where the scanner is installed. | N/A |
| Scanner version | Whether the scanner version is up-to-date or not. | When scanned. |
| Additional information | Additional information registered for the server. | When updated on |
Server Addition
A dialog box containing a form to register a server with FutureVuls or a link to the registration method is displayed.

Physical machine scanning
Detect vulnerabilities by installing the Vuls scanner on the server. If you have an account with administrative privileges, clicking the “Add” button will display the installation command for the scanner.
Paste Server Addition
Add a server to detect and manage vulnerabilities by pasting the results of a command for environments where the scanner cannot be used, such as a closed network.
Container Image
Import the scan results of Trivy’s container image to FutureVuls.
Container registry integration
Register Amazon ECR or GCP Artifact Registry.
Library on file system
Import the scan results of Trivy’s library on the file system to FutureVuls.
Pseudo Server
Add a pseudo server that detects and manages vulnerabilities without installing the scanner based on registration information.
By creating a pseudo server with the name of a network device and registering a CPE, vulnerabilities on various platforms can be managed.
The created pseudo server is registered with OS as pseudo.
When a CPE is registered, the server is scanned and updated daily at 2:00 or 18:00 JST, but manual scans can also be performed.
Pseudo servers are also subject to billing, like other servers.
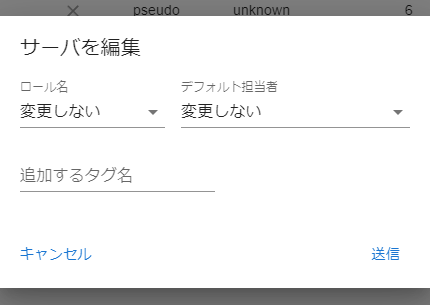
Server bulk editing
Select multiple servers and change their roles and default contacts in bulk.
SSM Scan
See SSM Scan to start a scan on demand for EC2 instances registered with AWS authentication information.
Server Second Pane
When you click on an item in the server list on the first pane, the second pane is displayed.
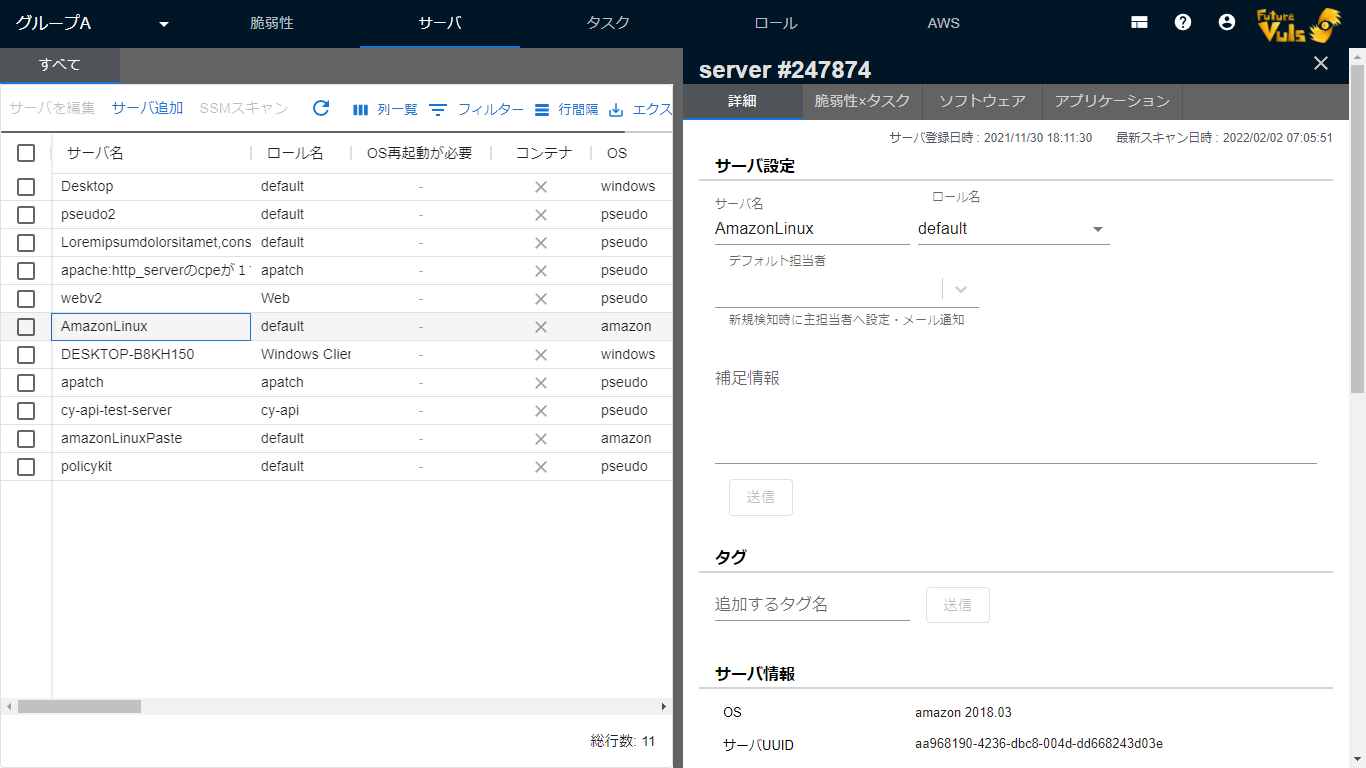
Detail Tab
In the Detail tab, you can check the details of the server.
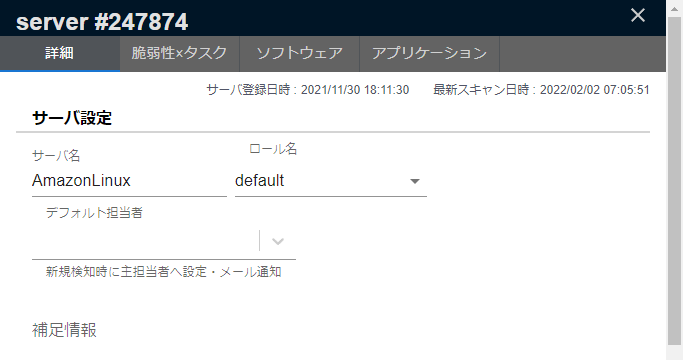
On the server details page, you can check server details, register tags, and delete servers.
Downloading SBOM file
Clicking “Download SBOM file” on the server details page will output an SBOM in the CycloneDX format.

Manual scan
By performing a “manual scan” from the server details, the detection process is re-executed using the latest vulnerability database at that time, and the vulnerability information is updated.
When rescanning from the screen, the previously uploaded information (such as OS package information) is used to perform the rescan, so the scanner on the actual server is not executed. If there are changes in the server configuration information, such as package updates, you need to run the scanner and upload it, not manual scanning.
GitHub Repository
GitHub provides a feature to detect library vulnerabilities as standard. About Dependabot alerts - GitHub Docs.
You can incorporate the vulnerabilities detected in the GitHub repository and manage them on FutureVuls.
For details, see How to integrate with GitHub Security Alerts.
Task Copy
You can update the task information associated with the server by copying it from other servers in the group.
When you add a new server with the same configuration as a server that is already registered in FutureVuls, you can synchronize information such as status all at once.
Follow the steps below to copy the task.
- Select the destination server to copy from the server tab and open the details screen.
- Open the dialog from the
Copy task information from another serverbutton at the bottom of the screen. - Select the source server and execute.

The tasks that will be copied are tasks that have been detected in common with the source server and have a status of NEW at the destination server.
Also, the task information to be copied is as follows.
- Status
- Priority
- Primary/secondary responsible person
- Scheduled execution date
- Hide setting
Delete a server
Once you delete a server, you cannot restore the status of tasks, etc. It will be registered as a new server if you scan it again with the same UUID.
Vulnerability × Task
Displays tasks and vulnerabilities related to the selected server.
The information displayed on the Vulnerability × Task tab is the same, but the order of the columns is different. Please use the tab that is easy to use depending on the situation.
Software
Software displays all software installed on the server, including software without vulnerabilities.
Please also see [Software] and [CPE] in the help page.
Moving a server to another group
“Organization settings > Settings > Move server information to another group…”
Server Copy
-
Copy Target
- Server Details
- CPE Information
-
Notes
- Organization owner authority is required to copy the server
- If the server is being used by a scanner, scanner settings must also be changed according to the dialog on the screen
- The original group’s server is not automatically deleted
- If there is a server with the same name in the destination group, it cannot be copied
Task Copy
-
Copy Target
- Task Details (only for tasks with NEW status on the destination server)
- Task Comments (only for tasks with NEW status on the destination server)
-
Notes
- Organization owner authority is required to copy tasks
- The original group’s tasks are not automatically deleted